Every day we offer FREE licensed software you’d have to buy otherwise.
Giveaway of the day — Silver Key 4.3
Silver Key 4.3 was available as a giveaway on September 26, 2014!
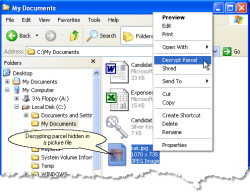
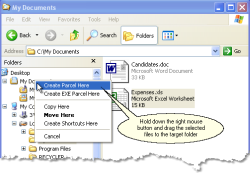
If you need to send sensitive data over the Internet you should encrypt it first. But what about the other side? The recipient will probably not like the idea of buying and learning some software just to decrypt your file. No problem here if you are using Silver Key.
Right-click the file or folder you wish to send and select the "Create EXE Parcel" command. Silver Key compresses and encrypts your data and adds a small decryptor program. Your correspondent does not need to install any decrypting program because the parcel already contains all the needed software. If your demands are higher, you can use the Silver Key Parcel Designer to create more advanced encrypted parcels. You can add encrypted and unencrypted comments, create shortcuts on the target computer, request opening a file after decryption, and even include an uninstaller.
System Requirements:
Windows 2000/ Server 2003/ XP/ Server 2008/ Vista/ 7/ 8/ Server 2012 (x32/x64)
Publisher:
Inv SoftworksHomepage:
http://www.kryptel.com/products/silverkey.phpFile Size:
12.2 MB
Price:
$29.95
GIVEAWAY download basket
Comments on Silver Key 4.3
Please add a comment explaining the reason behind your vote.




Ultimately a good idea, BUT it all comes down to the password and how easily - or NOT, the password can be discovered by whatever means (hacking, cracking, guessing, fluking etc.).
If the password allows the use of asterisks (*) and not all programs do allow their use, then the task of discovering the password can take a very long time indeed - especially if it includes more than one asterisk, and is also more than say 8 characters in total length.
The Gmail issue is an important matter, however it can be avoided simply by renaming the .EXE (for example to .xex) of course the user must have set up M$_Windows to see the file extensions.
Save | Cancel
For those who say that certain Email providers will NOT send ".exe" file attachments:
There is an easy way around this!:
Just remove the file extension ("Charity.exe" becomes "Charity") or CHANGE the "extension" name ("Charity.exe" becomes "Charity.txt") and then send it !!! You can give instructions in the email for the recipient to change the name back (if you have not already had the arrangement (previously) !!!
Save | Cancel
Chances are, that if you are sending an encrypted file to someone, you are probably doing it regularly.
You could simply setup a DropBox shared folder, then drag the file to your recipient's folder. It will automatically end up on your recipients hard drive without further ado.
And of course, DropBox is 256 bit military level encrypted automatically. And it's free!
Just saying.
-Mark
Save | Cancel
@ five - roman
Say again..i've sent exe files thru yahoo...you must not have ur settings right or have it filtered...but say u can't find the settings to change...couldn't you put the exe in a zip and send..of course u can...i've done it hundreds of times over the years..
Save | Cancel
This offering is Amateur Hour. In the States, many businesses use CRES (Cisco Registered Envelope Service). Once registered, you can use it (free) to send confidential info to someone else. Simple to use and Cisco is a well-known and respected corporation.
https://res.cisco.com/websafe/about
I'm not certain about laws governing its use in other countries or for for sending confidential info to/from other countries and the US but they do have a link for that info if you need it. I only use it in the US.
Save | Cancel
Does this software, like all other encryption software, have a backdoor for "security reasons"?
If so, what is the purpose?
Save | Cancel
Is this a dual-key system like PGP had? If so, then this is as secure as it gets, and is the reason the US government persecuted
PGP's originator, Phil Zimmerman, as fiercely as it did, back in the 90s. Sender and recipient can have two different passwords, and they don't need to know each other's. Part of the strength of the original PGP was that it allowed pass-phrases, i.e. it could contain spaces. You passphrase could be of almost unlimited length if you chose. I don't remember whether both parties needed to have the software, but anyway it was freeware so that wasn't an issue. And even with a command-line-only interface, it was still a runaway "best seller". Later it was bought by a then-major software company which has since disappeared, plus it ceased to be freeware at that time; then it was bought by another company that basically plowed it under, and it hasn't been seen or heard from since, AFAIK.
If this offering is that good or better - and encryption strength should have made some improvements over the years, as the maximum strength back then was 1024 bits - then if it's also stable, it should definitely be worth a try.
Save | Cancel
the activation is tied to hardware which means that it is not portable.
Save | Cancel
Ingvar wrote:
"A problem is that one is not allowed to send exe-files via gmail."
Quite a few others said the same thing. I'm a bit puzzled why if gmail and yahoo are the most popular email providers that none of our experts here have a workaround. -- Just rename the extension!
I suggest the extension be renamed ".morph" so when you see it you know that it was "morphed" and must be changed so you need to rename it back before use.
Another comment by Barry1 added that gmail and yahoo may truncate non-.exe files to trim trailing space at the end of attachments (they assume the file is plain text). The remedy for that is similar - just rename the file with an extension like: ".morph.pdf" -- Here the email will see the .pdf and think it is a document and leave it alone. You see the ".morph.pdf" and turn that back to ".exe".
You can give those instructions to the recipient in the body of the email.
By far the best comment everyone should take note of was from DislikesCensorship and he noted that Windows comes by default to "hide extensions" so you may not ever see what the actual extension is -- or even know one is there. The fix is easy, just uncheck the box where Windows Explorer's Tools/Folder/View menu sets the option for "Hide Extensions for known file types".
(I thought everyone did that the first time they logged into a new computer.) I never could understand why Microsoft would make that a default!
Now for the big news:
If email won't pass the file type you want and some email won't let you send large attachments (or receiver can't accept such). Then don't send stuff by email - use Dropbox or such services that allow large files and don't care what the extension is. They also have much better privacy settings for sharing what you want others to see and are accessible from non-Windows devices as well.
Does Silver Key have iPhone or Android versions to unpack Silver Key data?
Save | Cancel
I would like to use Kryptel from a USB drive. The FAQ section of your web site shows this is possible with a download... Is there a way of making this version portable? I would really like to try out this feature.
Save | Cancel
It is my understanding that to be FIPS 140-2 compliant, approved encryption must be done in a physically secure tamper resistant device and the device must be on the FIPS validation list. Your home computer is not one of those devices.
Save | Cancel
@#7. For email that do not allow sending .exe file, you can rename it to something like .doc and tell the other end to rename it back to .exe in the password message. Isn't that add more security? It is less work than give the other end to download a decrypter.
Save | Cancel
Silver Key USB 4.2 Edition Is Free. Whoever needs it, can download from this link.
http://www.techspot.com/downloads/6530-silver-key-free-edition-usb.html
Save | Cancel
#6
#30
According to some website, Inv Softworks LLC is a software developer located in St. Petersburg, Russian Federation in Russia.
Presumably Inv is an acronym for Invanov.
It is common for foreign companies to use a physical mail address in another country as a registered company front end. Sometimes numerous (say e.g. 100) other unrelated companies use the same physical mail address which can be just a small 20 square metres rental unit in a building complex. This is sometimes not a good sign.
Just because a company has a postal address in USA does not mean it will surely be an American company.
Save | Cancel
@everyone - You use a word/phrase that has meaning to both sender and recipient and is/has been known for awhile (you won't have to send a 'clue' or 'hint'). When I send emails with encrypted attachments my recipients know the password based on the greeting ("Hello" = "Superman", "Greetings" = "CallOfDuty", "How are you" = "ChuckECheese", etc.). This has worked well for me for decades. The level of encryption being used is the worrying point; this seems to have that covered.
*NOTE* The extremely paranoid can use something like "Hello" = "Qj60PaH2UmA5d".
Save | Cancel
NSA goes crazy when they see an encrypted file, they immediately make copy of it and will decrypted with their super computers when ever necessary.
Renaming an EXE to TXT or other format may create other problems at GMAIL, YAHOO and other providers, because they may truncate the file or remove the trailing bytes from the files.
I just uninstalled it, to much hustle.
Save | Cancel
I use 7zip. Its helpful in too many ways and its free. It can encrypt with incredible power. Many programs actually use 7zip to encrypt data. So it is pretty awesome at what it does. People suggesting Axcrypt, I think silver key is different.
On a completely different aspect, @Arturo, that is one excellent book. King is at the top of his game. Heard Matthew Mcconaughey is gonna be playing Randall Flagg in the movie adaption. wooooh...
Save | Cancel
One way to choose passwords to send along with the encrypted message is for you and the recipient to have a copy of the same book(s). Then use this method of in-the-clear to identify what the password is.
103rd page, 5 paragraph, 9 word. Or even send the p/w this way: 103-5-9. To make it even more secure have several different pairs of books to select from! i.e. 5-103-5-9
Of course you randomly select different books, pages etc for each message.
Save | Cancel
@ Andre Stoeff (Silver Key) - Yes! You're correct. My mistake.The file size limitation is a Windows' limitation. But the point is other software such as 7zip can create an exe file over that limit. Therefore it weakens the desire of purchasing the software if one needs to make encrypted exe files beyond the 4Gb limit. So if there was a way to get around that obstacle then it would give us more of an incentive to purchase the software.
Anyway...still fine software. Thank you.
Save | Cancel
Wow - wouldn't want to wade into THAT debate - not downloading - not voting - & thanks GAOTD & Inv Software (looks like a great product, but not one I would use or need - don't even have a way to test, sry) for today's offering. Have a great day!
Save | Cancel
Encryption has a huge market, now that its out in the open that the FBI and other secret polices from the world over snoop on the common man's life from under a microscope. Privacy means nothing. Anyway, this app works well. Not at all complicated. Much recommended. And Andre, thanks for the direct interaction.
Seems like a rainy day. Gonna make me some tacos and read The Stand. Nothing like horror on a rainy day.
Save | Cancel
@batsdude - No! The binary key should be given to the recipient at a previous time and not with the encrypted file. Then the recipient can use the key to open encrypted files when it is sent to them. I think it is common sense.
Save | Cancel
If you download email stripper ( it's free ) and then open any e mail that has been encrypted, cut and paste what's in the encrypted email, and paste it into e mails stripper, and click " strip, " email stripper will show exactly what the encrypted e mail says. No matter what Encrypt you use, this always works. That's one of the reasons I've never used an encrypted. Sadly, I'll have to pass on today's GOTD because there's two problems: Some mail services won't let you send an exe. file, and others that receive you're e mail would have to install the exe. file. And what's the number one rule with reading other people's e mail? Never, ever d/l ANYTHING.
Save | Cancel
RealBull: "One limit I have found was the exe parcels have a size limit of maybe 4Gb."
It is a Windows limit, it can't run too large executables. Such files can still be decrypted though.
TK_M: "Looking at your website though, you claim it is HIPPA compliant? That is quite a claim, but how secure is the data-as in what encryption is it using?"
Silver Key has FIPS 140-2 compliance mode, in which it does not use proprietory modules. Encryption is done with FIPS-certified CryptoAPI:
http://www.kryptel.com/support/fips_140-2.php
As to how secure is it, you need to ask FIPS who certified it. Encryption strength is always a matter of trust.
"hiding one of your parcels inside a jpg – Is that something that the program does itself (steganography), or a separate product?"
It's a standard Silver Key feature. And answering your other question: Silver Key parcel can be identified by its signature, so it is not steganography in the strict sense.
Save | Cancel
#7, you can always dump gmail. They are NOT the only free email/web based service around. I dumped all my gmail accounts when I switched to axcrypt and started sending .exe's.. Just make sure the person your sending it too has the PW to open the file.
This seems to work the same way. Worth giving it a try
http://www.axantum.com/axcrypt/
Save | Cancel
Sending the key along with the lock is useless, as what is the point of the encrypt in the first place. As one other commenter stated, yahoo wil not send any .exe files, but also have a size limitation anyway, thus defeating sending anything that way anyway, and I will not ever use the yahoo cloud system to send anything.
Save | Cancel
#6 Karl:
For the record, this is not an American software company, although they do everything they can to make you think it is.
Pacific Business Center
P.O. Box 34069 #381
Seattle, WA 98124-1069
USA
is a drop box for a Russian software outfit that we've had offered here many times in the past for many different programs.
A simple Google search shows [potentially] hundreds of "different" software companies using that same address.
Now that may not have anything to do with the quality or usability of their software. I'm just always leery of companies that lie about or hide their identity.
Save | Cancel
If you search in any browser: howtogeek.com send encrypted email
You can read a long list of similar software, free and otherwise.
Which one you like is a personal choice.
Google Mail has a built-in facility to send encrypted email.
If I have to, can I not send an encrypted zip?
MsWord has a built-in feature to encrypt a MsWord document, which we can send via email.
The larger question is:
Do ordinary home use consumers bother with encrypted email?
Why do we need it? Definitely not for all email we send.
For the rare 0.0001% occasion when encrypted email is needed.
Assuming some need it, what is the percentage take-up by the public.
Encrypted email should self destruct within a certain period. Or else it is always present for someone to slowly decode.
Save | Cancel
So you are sending someone an encrypted attachment that will decrypt itself once the enter the correct key? You mean like creating a 7zip encrypted zip and then making it self-extracting like using 7zip's "-sfx" to make a self-extracting archive? - Like many "zip" type programs can do?
Your version DOES make it a little quicker and easier to do if you are not too used to computers. Looking at your website though, you claim it is HIPPA compliant? That is quite a claim, but how secure is the data-as in what encryption is it using? Many types of encryption have been broken, or are proprietary and so not assessed for security.
It is a nice and easy program to use. Slightly quicker than having to make a zip yourself and then making it self-extracting. My only concerns are about HIPPA-compliance and how secure the encryption method is?
You have good "Quick-Start" page on your website, that answers a lot of questions that others might have.
http://www.kryptel.com/articles/sktutorial.php
It includes hiding one of your parcels inside a jpg - Is that something that the program does itself (steganography), or a separate product? As that opens a few more problems about it needing to be a very large jpg and a very small parcel for it to be credible for example.
Without wanting to get too technical, does your program have identifiable headers on the parcels, so a simple examination with a hex editor (or even opening the exe in notepad) reveal it is not really an exe, but one of your parcels?
Thank you for your help Andre.
Save | Cancel
I've been using this program for over a year. It's a useful and stable program. One limit I have found was the exe parcels have a size limit of maybe 4Gb. Going over the limit will cause problems and the parcel cannot be opened. Therefore it's impossible to send large graphic design files with this program. Other than that it never crashed from the numerous times I've used it. Yes, you can use 7zip, WinRAR, etc., but this program can create a binary key that the recipient can use to open the parcel without using a password.
Save | Cancel
@stoobee: Sorry, I don't quite understand what you mean. Intercepting the file will not give an access to its contents. The file is encrypted, so it is safe to send, or to store on a public server. No one can open it without the password.
Save | Cancel
While it may be possible to change the .exe to .exex or something similar, the time (and patience) required to explain to the average user (on the receive side) how to unhide extensions and change them from .exex back to .exe makes this a hassle.
With so many not just good but excellent programs already out there doing the same thing for free, I see no reason to leave my 7zip or winrar for a solution with the exact same impracticalities as the ones I already have.
Save | Cancel
If decryption were made available in the suggested way, could not a mam-in-the-middle hacker intercept the file, and have the same means as the intended recipient, to decrypt it? It is only encrypted as long as no one intercepts it between the endpoints.
Save | Cancel
So, kind of like using a password on a zip or rar file, and encrypting the names of the files then? Nicely enough this then works for Android, Mac, Windows, and Linux. Alternatively, use a PDF encrypter and take make the permissions of only able to be opened with the password.
Rar and Zip can then be emailed no problem, and most people Do have an archive manager to open it *shrug*.
Save | Cancel
Hi, Silver Key is a good idea and promoting good ideas by GOTD (naturally in shape of specific Programs) is always commendable. It educates and shines a light on how things can be done simpler and/or safer without dipping into Google. Followed as usual by other suggestions from fellow users and experts here, and today presence of Support from Vendor to answer certain questions - gives all in all cool and neat 'Package'!:)
I've been sending recently (via e-mail) some sensitive tax forms to family and have to admit - holding my breath.. How many times and in a hurry we simply focus on delivering such post, especially when time is pending, and are gambling (yes) that no one else can make use of it?? So I welcome today's Program as something I might try and use in specific circumstances, such as example I gave above. Thanks Inv Softworks and GOTD for this Program and.. highlighting (again) manner of safety when dealing with sensitive data in 'every day' mailing.
PS. I set shortcut to Silver Key on my desktop to open 'Program Group', as at first simply un-ticking every box just to check if Program was correctly registered - shortcut didn't work at all, so if anyone went that route - don't panic, find in Program Files in Silver Key Folder 'Complete Installation' and tick all boxes this time. I know, bit unorthodox..
Save | Cancel
Jim-1: "Kryptel needs a cross platform version that will work on both Windows and Android"
The most pressing matter for Silver Key is a parcel server, which should completely remove the problem of blocked exe parcels. It is almost ready and the next version will be able to send parcels through it transparently. After that we plan to add portable decryptors for Android. We are not sure about porting the whole program yet, it is VERY large.
Save | Cancel
@ Andre: Kryptel needs a cross platform version that will work on both Windows and Android. Then a user on a PC can securely communicate with another user on Android. The encrypted file should have no extension for better security and so it can be easily sent by email.
Save | Cancel
Cool little prog. I see it as being beneficial as an added layer of security process within my existing compression/encryption archive and delivery methods. Never wise to use only one method, but better to combine several methods, both hardware and software into your personal secure system.
Save | Cancel
Harry M: "While the basic idea is good, some other mechanism than EXE should have been chosen"
Silver Key can also produce non-executable parcels.
Chewy: "17.My first thought when I read the description was, who in their right mind is going to run an Executable file received via the internet?"
Yes, EXEs may be dangerous, and we recommend using non-executable parcels when possible. However in many situations sending EXE is a necessity, and it is not as risky as you make it sound. Silver Key can digitally sign EXE parcels to reduce the risks:
http://www.kryptel.com/articles/certificates.php
Save | Cancel
My first thought when I read the description was, who in their right mind is going to run an Executable file received via the internet? My second thought was, if they have to call you for the password, you just defeated the main reason for using eMail. How about sending an eMail that reads "Call me"... and just tell them what you wanted to put in the message? A nice idea in theory, but less than practical in my oppinion.
Save | Cancel
Sending an EXE over email is a horrible idea.
Many email servers either reject such email or delete the attachment.
While the basic idea is good, some other mechanism than EXE should have been chosen (maybe password-protected encrypted PDF?).
Save | Cancel
Never got as far as the registration phase, gave up to be honest possibly having a senior moment.
Not too worried as I tend to agree with #11 Marius, that is, what is the advantage over an encrypted compression program?
Compression programs are cross-platform, they are not blocked by Gmail, you can if you wish create a self extracting EXE file, if you use are RAR files you can hide the filenames.
#8 DislikesCensorship
When I had a non-booting system put the drive in the USB external container and extracted my files in a file manager.
Save | Cancel
I forgot to mention that renowned free 7ZIP is portable and can password protect zipped files. You need no additional pay software which gets outdated and whose producer you have to trust too as you wouldn't like to give away your data on a silver plate.
Save | Cancel
@5 roman
"... So you have to rely on file transfer services!"
This would rule out Silver Key 4.3 for everyday use. But perhaps no! If you rename the filetype to something non executable, e.g. "ixi" instead of "exe" and tell the recipient to rename it back again, it would pass the mailer's filters.
If somebody is so careless to let Windows hide extensions he should alter Windows preferences at once. But those persons won't use this software anyhow.
Please, could somebody trying this software try this easy turnaround too and tell us.
By the way you naturally should transfer key and file on different channels thus ruling out everybody besides great nations' intelligence or criminals having already infiltrated your computer.
Save | Cancel
Is this basically the same as sending a winrar archive with a password over the internet? What is the difference? Wouldn't winrar be better because it puts the exe in an archive and again you can't open it without a password?
Save | Cancel
Ingvar: "It would have be better if there was an free decrypter program that the receiver could download".
We do offer a free decryptor program - Silver Key Free Edition. It can be easily configured to disable unneeded options (encryption, for instance) and show only the 'Decrypt Parcel' command.
Save | Cancel
When I send exe-files via gmail I just rename them as txt or doc and tell recipient to rename back to exe
Save | Cancel
@RichU
Yesterday's call for help by RichU concerning "EaseUS Todo Backup Home 7.0" problems.
0 Try to boot in protected mode.
1 Save your valuable files elsewhere! Get some Linux based bootable medium (CD, DVD) perhaps from a friend or a computer magazine - they sometimes give several systems for choice. There are antimalware versions too: check your system!
Keep in mind that partitons/harddisks may have other names e.g. sda1, sda2, ... and USB media sdb1, sdc1, or other numbers and not C\: etc.
2 Copy your whole system to an USB harddisk with sufficiant storage and use folders C, D, etc. If you can't do this no additional advice from me is possible besides connecting your internal harddisk to an external USB-incasing or USB-SATA-adapter and thus ruling out hardware problems. Or as last choice try Linux based recovery software. But blowing up this advice perhaps is beyond the limits of moderator's patience and you seem to have internet connection elsewhere. So you can do some research yourself in forums.
Every Linux comes with some sort of explorer (there are two-Windows commanders available too). Normally it's sufficiant to click once on a harddisk icon to open partition etc. There is an option to mark everything. Copy by drawing to the other window, you are asked whether you want to copy or move (Choose copy!).
If somebody encounters problems it's always utmost helpful to tell about system configuration as e.g. UEFI based systems are more complicated to handle. But mentioning "Windows7" in your call for help tells me that it can't be UEFI.
By the way I haven't got same problems as I didn't ever try EaseUS Todo Backup Home 7.0. I only use a combined version of another brand with partitioner and imager in one program as I already have "installed" hundreds of programs, portable if possible and causing no registry problems.
Save | Cancel
A problem is that one is not allowed to send exe-files via gmail.
It would have be better if there was an free decrypter program that the receiver could download.
Save | Cancel
Installed and registered without problems on a Win 8.1.2 Pro 64 bit system.
An American company with address in the contact info : Inv Softworks LLC
Pacific Business Center
P.O. Box 34069 #381
Seattle, WA 98124-1069
USA
This installs the standard version, the Enterprise version has as additional features :
Command-line interface for automated encryption tasks
Native 64-bit processing
Utilizes multi-core processors to speed up encryption
Advanced Data Recovery feature allows restoring data from corrupted containers
FIPS 140-2 compliance mode (Google!)
The software has valid certificates from COMODO Code Signing CA2.
I simply repeat from the last offer, because it is the same..
The first interface is terrible, a small not resizable window with “wizard options”, made by somebody on the fly…
@ Inv-Softworks: Why don't you simply forget this first ugly options interface and build a complete "Silverkey" Interface with selectable options???
Well, I selected the "Advanced Parcel Designer", you can add files or "subtrees" - why not name it as all other do : folders???
You can change encryption parameters. "Crypto settings", which is renamed in the window to "Silverkey settings". Why not use the same expression?
After selected the (right) setting, you can create a "parcel", which is an self-decrypting executable - if the receiver has the right password of course.
This is done without problems. But... this could be done in a much better interface.
Does what it claims. It is basically a good idea to send private information in an encrypted way over the internet. It is basically a good idea to produce a self decrypting .EXE for the receiver. I generally dislike closed software in the encryption field. A matter of taste, of course.
There could be added some other ideas. A confirmation system, that a receiver received and opened the parcel, for example.
Uninstalled via reboot - no need for this kind of software
Save | Cancel