Every day we offer FREE licensed software you’d have to buy otherwise.

Giveaway of the day — Silver Key Standard 4.9.0
Silver Key Standard 4.9.0 was available as a giveaway on March 2, 2017!
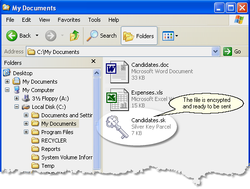
If you need to send sensitive data over the Internet you should encrypt it first. But what about the other side? The recipient will probably not like the idea of buying and learning some software just to decrypt your file. No problem here if you are using Silver Key.
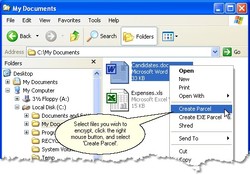
Right-click the file or folder you wish to send and select the "Create EXE Parcel" command. Silver Key compresses and encrypts your data and adds a small decryptor program. Your correspondent does not need to install any decrypting program because the parcel already contains all the needed software.
If your demands are higher, you can use the Silver Key Parcel Designer to create more advanced encrypted parcels. You can add encrypted and unencrypted comments, create shortcuts on the target computer, request opening a file after decryption, and even include an uninstaller.
Please note: the download archive includes the Portable USB version as well!
System Requirements:
Windows 2000/ Server 2003/ XP/ Server 2008/ Vista/ 7/ 8/ Server 2012 (x32/x64)
Publisher:
Inv SoftworksHomepage:
http://www.kryptel.com/products/silverkey.phpFile Size:
35.5 MB
Price:
$29.95
Comments on Silver Key Standard 4.9.0
Please add a comment explaining the reason behind your vote.



no issue on installing the s/w, it is very smooth.
try out and find that it is useful.
how to convince the receiving party that it is safe to open, it is a big problem.
anyway i like this s/w.
thanks, Inv Softworks & GOTD.
donald
Save | Cancel
Installed fine but key doesn't work for me. Anyone else having problems with this?
Save | Cancel
FWIW I think that maybe most of the time when people talk about encrypted communications nowadays they're talking about Android &/or iOS devices using apps with end-to-end encryption to avoid the possibilities of eavesdropping. Email is inherently insecure in transport [from you to the recipient], & IMHO attempts to fix that have never really caught on, though ProtonMail is gaining notice [protonmail[.]com], & I believe Google is working on solutions. Adobe also has secure document solutions for biz.
Without a method of secure communication the only alternative is to secure the message [or data etc.] in an encrypted package. The hard part is painlessly getting the encryption key securely to the intended recipient(s) -- the painless part is why many feel that PGP isn't more widely used.
Silver Key lets you create those encrypted packages, whatever you choose to do with them, e.g. upload to something like Dropbox, send as an email attachment etc. You might create a SHA hash & give it to the recipient along with the key to further ensure the package hasn't been altered or tampered with. Silver Key Enterprise edition can also use certificates.
RE: SHA hash -- wikipedia[.]org/wiki/SHA-2
As pointed out in the ad copy, encryption apps can have a ease--of-use problem, in that the recipient might need the encrypting software to decrypt what you sent them. Silver Key has the Option to let you create a .exe file that includes the decrypting software -- no app installation needed. Many people put an .exe file in a zip or 7zip archive when they want/need to send it as an attachment via email.
Why not just use something like 7-Zip, which was proposed in other comments? That's a question best addressed by the developer, though I could understand from a marketing standpoint if they did not want to mention alternatives. Otherwise take a look at the web site for Silver Key, and see if the software's features make it a better alternative while it's on GOTD.
Save | Cancel
I have to say that your software looks good and works fine as a normal install. But as a portable software it does not, for it only reads the settings files from ( C:\Users\User\AppData\Roaming\Inv Softworks\Kryptel Common Data\Settings ) instead of ( D:\SilverKeyUSB.4.9.0.2\Silver Key\Settings ).
Just because the software can be run from a portable drive does not mean that it is portable; portable means that it will keep all your settings and personal information with in the drive that it was run from.
You can try and work the Portableapps.com community and try and make it fully portable with there Launcher.
They are well known and can help if you need be.
Thank you for your willingness of letting the community to try test your software for free so that is this comments and feedback can help improve your product in the future.
Thank you and God Bless you all.
Save | Cancel
I"ve seen this type of software before, and offered here before. Forgetting the .exe problem, there are workarounds for that, does my recipient need a password to open the file? I'm assuming so, but if not how safe is this really? I've never used this type of software; I rarely send files in email, I've normally used a cloud storage system to transport files and the only thing my recipient needs is the password to retrieve said file. Just wondering how safe this really is; not saying it's not, just wondering?
Save | Cancel
JonE,
"I've normally used a cloud storage system to transport files and the only thing my recipient needs is the password to retrieve said file."
Ideally it should be encrypted before you upload to the cloud. There's also the question of how you give your intended recipient access to your cloud storage? If you send them the password or an invite via insecure email, you're really not any more secure than if you just attached the file to an email in the 1st place. As far as cloud storage goes, hopefully it's secure, but just by being stored someplace for whatever length of time, vs. passing through the pipes of the internet on its way to the recipient in an email, you might have a larger risk of attack or greater attack surface.
Save | Cancel
mike, I see your point.
Save | Cancel
This program sounds well and good but exe files are the most abused files for viruses, adware, etc. If encryption is needed for safe email communication then there are much better programs and services. PGP is a great encryption program that uses keys to encrypt/decrypt, and there are a few email services, like proton-mail, that are encrypted/decrypted at each end.
Save | Cancel
But ... when you send "sensitive" information, you send along the key(.exe) ??? ... ???
Save | Cancel
I would rather bring the document that needs to be encrypted into a password protected zip-file. This can be opened by the recipient, no matter what operating system or other software he uses. To create such a password protected zip-file on Windows I recommend the free 7-zip.
Sending an exe-file like what this program offers is not ideal for three reasons:
Firstly: exe-files can only be opened on Windows
Secondly: often exe-files are not allowed as email attachments and are filtered out on the recipients side
Thirdly: executing exe-files can be dangerous in regards of computer viruses, so many recipients hesitate to execute them
Save | Cancel
I did install it in Win10-64.
I made a picture(PNG and GIF) and hide the PNG in the GIF:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/SilverKey490_20170302/GOTD.gif
The hiding:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/SilverKey490_20170302/VerbergenBestand.png
It can be viewed and edited.
And opened with today's software with ww: 20170302, then there is the other picture:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/SilverKey490_20170302/GOTD.png
This picture I also hide in a TXT and that went not fine:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/SilverKey490_20170302/Tekst.txt
Save | Cancel
Seems to be the same as FREE SafeHouse Explorer which can also send encrypted files that can be open without the need of the program installed by the receiver.
http://www.safehousesoftware.com/SafeHouseExplorer.aspx
Save | Cancel
Is this program HIPPA/Hi-Tech Compliant?
Save | Cancel
The license doesn't seem to work for the portable version. I run Silver Key.exe (after extracting SilverKeyUSB.4.9.0.2.zip, and keeping the extracted contents in the same folder), choose "Activate using your customer ID code", enter the code, and it says, "No appropriate license found."
Save | Cancel
Hello,
please note that this version needs to be installed on USB.
Please follow the instructions provided with the portable version.
GOTD team
Save | Cancel
Helen, Well, that sounds weird. Any portable software is supposed to work "without installation" from any drive/folder/directory; else, don't call it portable!
Save | Cancel
Hello,
it is for installation on external (USB) drives.
Save | Cancel
mukhi, Extracted to the root of a USB and it went fine with the registration:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/SilverKey490_20170302/RegistratiePortable.png
A program, Licensemanager is started:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/SilverKey490_20170302/Internetcontact.png
Save | Cancel
mukhi, I think you're mixing up the terms "Portable" and "Standalone". I'd say most, if not all, "Portable" software I've seen is "Standalone", but "Standalone" is not necessarily "Portable". By definition "Portable" software needs to be installed on a "Portable" device, most often "USB". That's not to say that I haven't seen software defined as "Portable" that could be installed on a "DD" or "SSD", but that is either exception, not the rule, or the software was improperly defined.
Save | Cancel
Ootje,
you are a good support personnel.
it is a eye-opener to read your comments.
thanks, i learnt a lot from you all the while.
donald
Save | Cancel
JonE, I think it's you only who is trying to "define" something...
According to Wikipedia:
A portable application (portable app), sometimes also called standalone, is a program designed to read and write its configuration settings into an accessible folder in the computer, usually the folder where the portable application can be found. This makes it easier to transfer the program with the user's preferences and data between different computers. A program that doesn't have any configuration options is also a portable application. This type of application can be stored on any storage facility, including internal mass storage, a file share, cloud storage or external storage such as USB drives and floppy disks – storing its program files and any configuration information and data on the storage medium alone. If no configuration information is required a portable program can be run from read-only storage such as CD-ROMs and DVD-ROMs. Some applications are available in both installable and portable versions.
According to a famous portable software site:
What is "portable"?
In recent years, the term "portable" has quickly come to be associated with apps that you run off a USB memory stick. However, to me, "portable" has always meant that I could easily move apps from one machine to another without too much incovenience. In fact, in the earlier days, I had my portable apps in a separate partition on the harddisk so that when I reinstall or upgrade Windows, I didn't have to reinstall/reconfigure my favorite apps. So in my mind at that time, portablity didn't involve a removable storage device at all...
To summarize, I have learnt that the ideal definition of "portable" means:
It must run without installation.
It must run on older versions of Windows which might not have been updated.
It must not have any coupling with Internet Explorer, audio/video codecs, DirectX etc.
It must not write settings to the registry or local filesystem.
It must not leave any trace on the host machine at all, even when the app crashes (hereby referred to as "stealth").
It must run with guest access rights.
It must be able to compensate for USB memory stick drive letter changes.
Save | Cancel
Ootje,
w/o reading this comment, i don't know have to registered the usb version after installed it on the usb drive.
i thought all are taken care when handling the main s/w on my pc's system.
many thanks.
donald
Save | Cancel
mukhi, Just proving that all kinds of software have all kinds of perceptions and definitions, by all different kinds of people. Not necessarily making me correct or incorrect.
Save | Cancel
JonE, I understand. I also understand that there are exceptions (like some "portable" software that work only from an ext. USB drive, or some of them don't even have the "stealth"). However, to me, a portable app should have the ability to be "ported" even without an admin privilege.
Save | Cancel
donald, when the portable is made form the installed main-version, then the activation will be done, sometimes.
In this case, the main version on the hard-drive is installed and the USB-version has it own installation. Therefore it had to be registered separately, just by starting the USB-version and fill in the code.
I ordered sometime ago a portable version of a program, an uninstaler. That program can be move form drive to drive, from usb to usb and is always registered on my name. Yesterday I placed it on a different Windows and it worked ok.
Just to make things simple: different software-maker -> different registration methods.
Save | Cancel
mukhi, That's a good idea of a portable, 99,9% right.
but ..
"It must not write settings to the registry or local filesystem.
It must not leave any trace on the host machine at all, even when the app crashes (hereby referred to as "stealth").
It must run with guest access rights."
--
I bought a uninstaller program, portable. The map containing this program can be place anywhere, USB, HDD ..
But it will change something in the main Windows; it can uninstall program's in that Windows. That the meaning of this program. Therefore I bought this program to help peoples with their Windows.
Also there are some program that removes malware, some of them are portable. But also then there are changes because of the nature of these program's.
The other portable's should only be called portables, as they meet the references as you described.
Save | Cancel
Any one opening a .exe file coming through an email is potato, and if they work for my company would be fired on the spot. What I would like to know is how did an .exe file get pass my security suite that protects the email server?
Save | Cancel
Sounds like a good idea, however... many ransomware detectors may have problems with this. I know mine is set to go off any time it detects encryption or decryption.
Save | Cancel
Many companies security systems block exe files... Not a good choice of container.
Save | Cancel
Many email clients don't allow .Executive to be sent you could always change the .Executive extension to something else but then you would let the recipient know. By sending them an email informing them of this. Which means extra effort on both sides and defeats the object. A rather pointless piece of software for most people.
Save | Cancel
DaveC, FYI .exe = Executable
Save | Cancel
BobbyA, yeah I know, think the spell checker on my tablet tried to correct the .exe and as I was preoccupied at the time of writing I didn't notice, but like you I'm sure most people knew what it was meant to be.
Save | Cancel
No Win10 support?
Save | Cancel
Tony, I worked in Win10-Pro-64 and it worked fine
Save | Cancel
Tony, What Bob said; if it works on 8, it most likely is going to work on 10. Give it a try, you can't mess anything up and if it doesn't work just uninstall it.
Save | Cancel
1. Exe-files GMAIL-mail are not accepted.
2. How is this program better than the archiver, which can also encrypt files, file names?
3. I have not seen a great program (even from the toll), which can crack passwords to encrypted files. The password can be in any language in the World, plus special characters.
Save | Cancel
Dimma, the popular free emails dont accept exe file. But i hope you can dropbox etc.
Save | Cancel