English
Every day we offer FREE licensed software you’d have to buy otherwise.

$12.00
EXPIRED
Giveaway of the day — Jade Encryption 1.0
Jade Encryption is a advanced encryption utility.
$12.00
EXPIRED
User rating:
79
97 comments
Jade Encryption 1.0 was available as a giveaway on December 4, 2016!
Today Giveaway of the Day
Apeaksoft WhatsApp Transfer is professional data transfer software.
Jade Encryption is a advanced encryption utility for the Windows platform, which provides simple and easy to use encryption for any purpose.
System Requirements:
Windows 7/ 8/ 8.1/ 10
Publisher:
Morshead SoftwareHomepage:
https://www.morshead.org/2016/11/27/jade-encryption/File Size:
545 KB
Price:
$12.00
How would you improve Jade Encryption 1.0 ?
No similar feedback found. Feel free to add yours!
Comments on Jade Encryption 1.0
Thank you for voting!
Please add a comment explaining the reason behind your vote.
Please add a comment explaining the reason behind your vote.
You can also add comment viaFacebook
Facebook comments
iPhone app giveaways »
$1.99 ➞ free today
$3.99 ➞ free today
$1.99 ➞ free today
Get this special numpad keyboard to enter numbers with ease in any app on your iPhone or iPad.
$0.49 ➞ free today
PDF2JPG is the ultimate solution for converting PDF documents into high-quality JPG images quickly and easily.
$0.99 ➞ free today
Android app giveaways »
The global bass booster and the equalizer enhances the sound quality of your Android device.
$1.99 ➞ free today
Want to get experience and emotion from driving a real city train in the metro simulator?
$0.99 ➞ free today
An alien ship has taken possession of multiple cities on planet earth, deploying countless robots.
$2.99 ➞ free today
If your device has low sound, use Volume Booster and Sound Amplifier to make your device super loud.
$1.99 ➞ free today
$1.99 ➞ free today

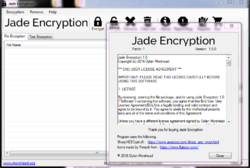

Thanks for the feedback, the next version will contain a bunch of new features that are planned.
The following features are planned for now.
password protected application.
context menu integration.
encryption plugins.
language packs.
Portability.
options to prevent deleting files automatically, in the event something goes wrong.
I've also got planned a FREE Edition with some limitations, (IE 5 file limit) so those who lose access can use the free edition.
I've currently working on Patch 2 which contains some extras and minor bug fixes.
Tomorrow I'll be giving out 20 serial numbers to the first 20 people who like the official Facebook page.
https://www.facebook.com/jadeencryption/
In the event people want to contact me, just for general questions or feedback, you can use the following
https://www.facebook.com/jadeencryption/
https://forum.morshead.org/
Thank you all for your feedback.
Save | Cancel
Minor updates are covered in the 1.0 version, however with the 2.0 version, you can request a free upgrade if you have the serial number from this version.
No main features will be added to 1.0, just bug fixes and some additional extra features.
Save | Cancel
Good job you have done.
Umm... Next time you high rez images for the icons
~Timo
Save | Cancel
161204
thought netframework 4.6.1 was mid july of this year; does one still need 4.5 ?
Save | Cancel
bubu, I wouldn't think you would, but if it crashes while encrypting, that would be the reason.
Needs 4.5+
Save | Cancel
@Dylan,
Please answer HJB's question.
Its been there for ages!
Save | Cancel
This program is very ok.
Save | Cancel
I would suggest you look at VeraCrypt
Save | Cancel
BernardZ, Veracrypt is nice :)
I personally use it myself.
Save | Cancel
This is VERSION 1.0. Think I will wait for the next version or maybe it is already out and we are being offered 1.0. Being a retired SOFTWARE ENGINEER, I know how these versions work. BUT, thank you GOTD!
Save | Cancel
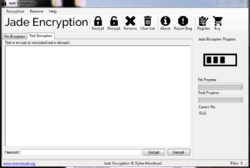
The UI has some issues: the menus lack underlined accelerator keys, the text area in the "Text Encryption" tab lacks a right-click menu and, most problematic of all, there's no obvious ways to add files to the file list in the "File Encryption" tab.
A bit of experimentation shows that you can add files by dragging them onto the list from an Explorer window, but the UI gives no indication of that and there's no alternate means of adding them provided.
This is compounded by the fact that there's no instructions provided, as the program lacks a help system.
Also, when you encrypt a file, the program deletes the original but there's no warning that it does so nor is there any means provided to created an encrypted copy of a file without deleting the original.
The program adds a .aes extension onto the end of the filename when creating a encrypted version of that file, but its installer does not associate that file extension with the program nor does associating it manually do you any good as the program does not support being fed a filename on the command line. As such, any time you want to decrypt a file, you have to both manually start this program and open a Explorer window (or equivalent) on the directory containing the file and then drag the file from the one to the other. Needless to say, this is extremely awkward.
There are also some other oddities:
- The "Register" command remains in the menu and toolbar even after the program is registered.
- You can add the same file to the file list multiple times, even though there's no reason to allow this.
- You can tell the program to encrypt an already-encrypted file and it will tell you that it has done so, but it doesn't actually do anything (i.e. the file will still be encrypted with only a single layer of encryption with the original password).
- Likewise, you can tell the program to decrypt an unencrypted file and it will tell you that it has done so, but it again doesn't actually do anything.
- The password dialog contains a "generate password" feature but you have to set the number of characters via a slider and it bizarrely defaults to 0 characters. If you click the Generate button without moving the slider, nothing happens. It makes no sense for that slider to even go down to zero much less default to that.
- While the "generate password" feature is embedded in the password dialog, it doesn't actually use the generated password unless you manually copy and paste (or retype) it into both password fields.
- It uses the same password dialog when encrypting and decrypting, which means that, when decrypting, you're pointlessly forced to enter the password twice and the unnecesary password strength display and generate password feature are still there.
Last but not least, there doesn't appear to be any information provided as to the encryption routines used, at least not beyond the hint provided by the .aes file extension.
Overall, I'm afraid the software seems rather half-baked.
Save | Cancel
I badly need not encryption
but a strong, working free
decryption program, to
decrypt lost password to
a True Crypt file.
Please- give me any
sugestions
Save | Cancel
Mary, the whole point of encryption is to make it impossible (or as close to impossible as is feasible) to do that.
You're not going to find a Truecrypt-cracking program.
Save | Cancel
Experimental version, no real AES key used. OK to encrypt unimportant data only.
Save | Cancel
Why would I want to tie up my files in an "encapsulated" vault that has to be opened. I want my files individually encrypted so I can copy them wherever.
Also a note on "TrueCrypt". After a year of trying, the FBI gave up on attempting to crack a hard drive that had been encrypted with TrueCrypt. * That's why they say it's "not secure". * Because they don't want you using it. Version 7.1a is the last "real" version. Do NOT use 7.2, it has a back door. People are liars. Version 7.1a was and still is, solid and stable. It had not been modified or updated for 27 months at the time of the panic announcement. Suddenly overnight it's "not secure"? BS. The feds bought the two guys off, and set them up on an island with babes and drinks for the rest of their lives. Use it, it's secure, but find a copy of 7.1a. And use a password that is 13+ preferably 16-20 characters, and you will be safe from brute force or others, until well after you're dead. You can use it for a complete device, or single files. Also has a hidden vault within for plausible deniability.
Save | Cancel
Why bother encrypting if Windows creates and holds a "Shadow Copy" ?
Save | Cancel
It does what it says, I have no complains. And I can use Bandizip to decrypt 9.11.jpg.aes it'll ask for the password.
Thank you!
Save | Cancel
ew, Thank you :P glad you like it.
Save | Cancel
Dylan, welcome :).
Save | Cancel
ew, Any extra suggestions? or features you'll like to see?
Save | Cancel
Dylan, I think context menu integration..don't know what extras I want in the software itself yet.
Save | Cancel
Dylan, oh yeah it'd be nice if it wouldn't delete original file after encryption is done..and when i'm setting password, i type it in the first field then i hit TAB and it skips the pass confirmation field goes to the last field, can it go to confirm password after pressing TAB in the first password field?
Save | Cancel
ew, I could add that as a setting, by default it won't delete the file.
Save | Cancel
Dylan, ok I can't think of anything else now :).
Save | Cancel
Dylan, it's good to see you as the developer actively responding to our comments. I think that how it should be on giveaway.
Save | Cancel
ew, :P
Save | Cancel
ew, Glad people are liking it though, I know it's not perfect, but it's only the first version, has a long way to go still.
I don't mind critics, either, without them, I wouldn't be able to improve onto this creation of mine.
Save | Cancel
ew and Dylan are stage names to prop up their own software presented here today.
Save | Cancel
Dylan, Yes Dlyan; make it compatible with XP; don't be like Microsoft - Support XP. There are still a lot of XP users out here. Till then I'll keep it for when I get Windows 7; if that happens before I kick.
Save | Cancel
Dylan, when should we expect an update and will it be free it we have this giveaway installed?
Save | Cancel
ew, Minor updates are covered in the 1.0 version, however with the 2.0 version, you can request a free upgrade if you have the serial number from this version.
Save | Cancel
Dylan, What I'm saying is that, there won't be any major features added in 1.0, but It'll have updates and fixes provided free of charge.
Those holding a valid licence for 1.0 can upgrade to 2.0 for free once It's release.
Save | Cancel
Dylan, ok, i see.
Save | Cancel
Perfect for when I e-mail my wife to pick up milk on her way home. We don't want information like this getting into the NSA's hands much less Julian Assange. I could just imagine what would happen if they knew I wanted whole milk instead of 2%.
Save | Cancel
I see what you mean.
Milk might be a code word for some weapon of mass destruction.
Whole, 2%, 1%, and skim could be quantities you want to buy.....
Save | Cancel
J Johnny Juice, Negative 6, people here take life too seriously. You got it.
Save | Cancel
I love this software, would recommend.
Save | Cancel
I forgot to mention, https://postimg.org/image/egxexj28h/
Won't even compile for the platform 4.0, so I'm literally not at fault here.
It's a .net problem
Save | Cancel
Even before windows came about, there was a software about 5KB each called: encrypt and decrypt they worked in DOS, they still work. Now put them in a GUI interface and there you have it, you can call it jade or diamond, it is the same software and principle. The passwords were saved inside the encrypted file and with HEX editor you can find it easy.
Save | Cancel
corry, try to find password with HEX Editor for a file encrypted with Jade Encryption, I bet you can't.
Save | Cancel
That's not how modern encryption works at all, not even jade will write the password to the file. That's a stupid thing to do, It's no longer 1989.
Save | Cancel
Dylan, This software is not secure at all, the passwords are written in the encrypted file without AES key.
I'm afraid corry is write. Please tell us what is the encryption key, that is, if you know where the password is written for later comparison and in what form.
Save | Cancel
ew, Do not be so sure, please tell me if you know if any AES keys are used and in how many bits, if you can not find it, corry is correct.
Save | Cancel
Maria, extraordinary claims require extraordinary evidence.
Save | Cancel
According to this forum feedback, the Jade Encryption software seems troublesome.
Kryptel is better, has context menu support and is offered on Giveawayoftheday from time to time.
Kryptel supports XP in addition to other Windows OS.
Save | Cancel
In the "Where have they gone" department, looks like Ashraf - who reviewed regularly on this site years ago - has his own giveaway site: http://sharewareonsale.com/s/free-winutilities-professional-edition-29-95-value
Now where's Karl??
Save | Cancel
J Johnny Juice, I've been getting programs from that site for about 3 months now. They have some nice giveaways. I did not realize it was "THE" Ashraf. Good to know.
Save | Cancel
Ashraf has had that site for years, even while he was reviewing here. It was after he and his wife had a baby that he stated he no longer had time to do both and would stop reviewing here. Just FYI.
Save | Cancel
jboy, it seems unlikely that Ashraf has much if any connection with the dot.tech and sos websites nowadays, judging by their quality. As to reviewing GOTD giveaways, it was great while it lasted (Bladed Thoth was first, then Ashraf, then Karl) and thanks are due to GOTD for facilitating those independent reviews. It is however an incredibly time-consuming task so no surprise that no-one is presently able to do the reviews.
Save | Cancel
Yeah, I remember that - you could click on a link for a more detailed software critique.
Save | Cancel
J Johnny Juice,
As long as we're being nostalgic, where's Giovanni? He always had a few free alternatives to the day's offering.
Save | Cancel
Stuart, quite possibly but the SOS daily email still is signed by him and a few months back when they modified their download method, he did the write-up explaining it.
It is time consuming and life goes on. I try to review when I can but I don't have the technical knowledge, like many here do, to really be constructively analytical about any software.
Karl seemed to have just dropped out of site.
Giovanni was a little too impressed with himself and seems to have disappeared when folks started calling him out for that.
Happy holidays!
Save | Cancel
Old Programmer's Mantra....
If at first you don't succeed - call it version 1.0
Save | Cancel
Robert Maguire,
Except Borland started with V2. ;-)
Save | Cancel
I did work on a new Win10-64 Windows.
It looked aright BUT:
if you encrypt text, you have to type the password at the bottom:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/JadeEncryption10_20161204/TekstEncrypt.png
When encrypting a file, you have to drag it into the program and then click on the Encrypt-button at the top:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/JadeEncryption10_20161204/BestandEncrypt-1.png
After the first time entering the password, you can not press one time on the TAB to get the next input-field.
3 or 4 times later it is on the right field. Developer: look at the source code and fix this.
Later on the original file is gone and replaced with a .aes:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/JadeEncryption10_20161204/BestandEncrypt-2.png
This should be in the documentation.
And encrypting a file twice(with 2 different passwords): it looks something goes wrong.
Also when opening a encrypted file, there is also something missing or cannot be found:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/JadeEncryption10_20161204/Missing.png
And the program should use "SharpAESCrypt.dll" according About:
https://dl.dropboxusercontent.com/u/10366431/_GOTD/JadeEncryption10_20161204/About.png
But when opening the file with HexEdit "CREATED_BY SimpleCrypt":
https://dl.dropboxusercontent.com/u/10366431/_GOTD/JadeEncryption10_20161204/InhoudAES.png
Save | Cancel
Ootje, SimpleCrypt was my previous open source project. (this project is based on that)
The reason for it saying missing dll, is it doesn't have support for windows shell support yet.
Save | Cancel
Can I use it on a thumb drive independently?
Save | Cancel
Captainn, It's possible, but the licence sticks to that one machine.
Copy Everything from C:\Program Files (x86)\Dylan Morshead\Jade Encryption\ to your flash drive.
Make sure the machine you want to run it on is either windows 10 or has at least .net framework 4.5 on it.
Save | Cancel
So many problems... Why should I trust my encryption needs to an undocumented version 1 app? There are no details about the encryption strength or cipher. For all I know it could be ROT13. And I need NET Framework? Wrong. So with a system crash, there's no ability to decipher using a USB key or CD?
Best to keep your encryption needs covered w 7zip 256 AES. Simple, reliable, and decipherable with nearly all AES tools.
Save | Cancel
Talleywhacker, Well if you don't trust it don't use it, that being said It does use a open source library, you could always compile your own version of it, and interchange the dlls with that version.
https://www.aescrypt.com/sharp_aes_crypt.html
Save | Cancel
Dylan, In future versions, I'll include the source code to SharpAESCrypt along side of it. Might even write a plugin manager so you can use your own encryption library with it. I understand your fear about closed source software though, I'm a guy who uses veracrypt ;)
Save | Cancel
Official Facebook Page.
https://www.facebook.com/jadeencryption/
Save | Cancel
Comment to developer really.
Since the addition of a warning on the free encryption program called truecrypt (which I still use, I don't beleive the warning) I always look out for another. Unfortunately for me this one has a long way to go. It seems you need a computer idiot who thinks he's a budding nerd to check yours out.
Someone like me. I did this:
I used Jade to encrypt a simple text file. Went to my file manager and looked for the text file "readme.txt" it had gone but there was a file called "readme.txt.aes" which I have never seen before (of course I knew what it was but may not in a week or so). Anyway I double clicked on it and was told there was no application that would open it. Now when I see a readme file with two suffixes one of which I recognise I delete the sufix I don't recognise (I can always put it back again) then double click it to see what it says. So I changed the filename of "readme.txt.aes" to "readme.txt" (as one might) and double clicked it - to cut a long story short having done that, no matter how hard I try using Jade or otherwise I appear to have lost my text file forever. Yes I behaved like an idiot but I need my software to be idiot proof. Enough said. Hope this is of use. Thanks for giving it to us.
Save | Cancel
David Murphy,
The file "readme.txt.aes" was created by encrypting the original "readme.txt".
If you open this new file with the GOTD-program and decrypt it, you will get the original file back.
AND do not test software on originals: make copies and test on that. Better safe than sorry.
Save | Cancel
Ootje, Thanks, yes I tried that and it works. But if you change the "readme.txt.aes" filename to "readme.txt" look at it in a text editor. cancell out of the text editor without changing or saving then change the filename back to "readme.txt.aes" and then try to decrypt you get a message from the decryptor saying something like "the header of the file does not....." something and would go no further. (Can't do it again to see full message have uninstalled). Could be wrong but thats what I think happened.
So what I am thinking is there are some general file management actions you can perform on the encrypted files, like reading them in a text editor, that can result in making them unable to be decrypted. Also if I remember correctly when I read the encrypted file in the text editor the header of the file gave me a clue to what created it as does the .aes in the filename.
I encrypt files so I can send them to others safely, or carry them round on a chip and not be scared of loosing the chip etc. So the file has to be robust, attackable, and renameable, and then still be able to be decrypted by he who has a password.
ie If I created a truecrypt Volume and encrypted it as a single file (the original might contain a number of files) and called it "mysecretstuff" and i wanted to send it to someone I could happily just rename a copy of the file as "readme.txt" and send it. Anybody seeing it with that name would probably ignore it or open it using windows notepad (most computers would too) and all they see is random characters with no idea, not only of what the password is, but also no idea that they might need a password and not even any idea of what program was used to create it. Thus there is a tripple lock and provided the file is not actually corupted it will still be accessable to someone in the know.
I agree that one should test software on copied files in a safe environment. (I actualy tested it on the readme file sent with it by GAOTD) but at some point you will use it for real and the nature of encrypted files is that they are secret so one would tend to keep the encrypted file and copies of it and get rid of the original for absolute security. I would not feel confident if I thought that there is any possibility that an unrelatted file management task might make my vital secret data unreadable or be happy to keep a non encrypted copy on my pc.
Save | Cancel
David Murphy, i found that it's possible to use Bandizip Archiver to un-encrypt an encrypted file, i don't know if other Archivers will do, in this way you have the context menu entry of bandizip in Explorer. Of course you have to know the password you set.
Save | Cancel
David Murphy, you most certainly should not still be using TrueCrypt as it contains a severe unpatched security vulnerability that can compromise your system by allowing an unprivileged process to gain administrator access via the TrueCrypt driver.
You should switch to either Veracrypt or Ciphershed, both of which are forks of TrueCrypt and both of which have that security vulnerability corrected.
Save | Cancel
Jim Stone, Thank you, that is very useful and gets me more up to date.
Save | Cancel
if i use this to encrypt a file, then the time limit expires, can i still access the encrypted file?
Save | Cancel
clas, You can, use https://www.aescrypt.com/sharp_aes_crypt.html
Save | Cancel
Dylan, Whoops, I meant. https://www.aescrypt.com/
It uses the AES format, and is completely works with aescrypt.
Save | Cancel
and pls add password feature while we open the app.
Save | Cancel
Damar M., I'm adding that on my todo list for version 2.0
Save | Cancel
It's useful. But I think the UI needs to be improved. Especially for the app launcher icon, it looks blurry.. And pls add more features.
Save | Cancel
Damar M., What features would you like to see implemented?
Save | Cancel
I've currently got language packs planned, minor bug fixes currently.
Save | Cancel
Dylan, maybe built in file explorer? and dark & light theme options, and remove the register and buy button after user was registered, and built in archiver.
Save | Cancel
Damar M., Icons are crystal clear ... Put your glasses on!
Save | Cancel
Ok tuyệt voi
Save | Cancel
oh the reason it's not working is I had to upgrade to .net framework 4.5
-The Daves
Save | Cancel
.
Would you kindly describe the program's features and benefits?
Thanks.
.
Save | Cancel
Peter Blaise, AES 256 bit encryption, Text Encryption, easy to use drag and drop encryption.
Some of the benefits are that you can use it to encrypt a large amount of files at a time, supports folder encryption if you drag a folder into it.
Save | Cancel
Jade Encryption is a advanced encryption utility for the windows platform which provides simple and easy to use encryption for any purpose. ............ can I use it to make breakfast, look after the baby, feed the dogs?
Save | Cancel
Nigel, any purpose meaning anything you want to encrypt, if you want to encrypt your dog food, you can scan it with a scanner, and encrypt the scanned image.
That being said, most software will not do those things for you. :P
Save | Cancel
Dylan,
As to the software under review, Jade Encrypton 1.0 :
A. Since the software is dependent upon a feature that may or may not be continued in net framework, is there a risk that, one will find that when he goes to decrypt, the process will fail?
B. In the use of software, such as this, if one encrypts a file, emails it to someone else, what is the typical manner in which one communicates to the recipient the manner i which to decrypt the file?
C. If one has a computer failure, and must rescue data files, the rescued file may nevertheless be inoperable. I suspect that this might be ever more so the case if the file is encrypted. Am I correct? What are the tried and tested ways of safeguarding against this, aside from archiving a copy of the software and the encrypted file?
Save | Cancel
HJB, Ok sorry for the late reply.
A. You can still decrypt files in Jade Encryption with other tools, such ases AES crypt.
B. I'm not too sure, just tell them to use AEScrypt.
C. Yes and no, depends if the file has actual damage or not.
Save | Cancel
Hello, I'm the developer for this software, It appears that .net framework 4.0 is causing the actual application to crash.
You need to download .net framework 4.5 in order for it to work properly,
This isn't a fault of the developer, but rather a feature we use that was only implimented in 4.5 and above in .net framework, as the application is written in C#
Save | Cancel
Dylan, https://www.microsoft.com/en-au/download/confirmation.aspx?id=30653
Save | Cancel
Dylan,
Thanks for today's software. A couple of quick questions. Firstly how long is the licence for and if/when it expires what happens to any files encrypted?
Save | Cancel
krypteller, Well It's not directly my fault, just human error, I used a second machine to compile and test the software, and by default that version of visual studio compiles to 4.0, by default something I missed until after launch.
It completely missed testing, as all the machines and testers had updated windows 7 with .net framework 4.5, but I've listed .net 4.5 as the version needed on my website.
Because of the features not being supported in 4.0, and having 4.5 on all the machines, it didn't appear as a problem, until I noticed a bunch of people having issues.
Save | Cancel
Well, I just looked into the issue, that's not the problem, I was looking at an earlier version.
The current version (the one on this site) is compiled for 4.5.2 and that is the target framework.
http://stackoverflow.com/questions/15113873/does-net-4-5-include-net-4-0
https://s14.postimg.org/hqqpxqght/lol.png
So as I said, I'm not at direct fault. 4.5 is literally an upgrade, and is backwards compatible with 4.0. so it'll crash if 4.0 uses a feature that is only in 4.5
Save | Cancel
Dylan,
I forgot to mention, https://postimg.org/image/egxexj28h/
Won't even compile for the platform 4.0, so I'm literally not at fault here.
It's a .net problem
Save | Cancel
DaveC, uses the aes format, if it expires you can still decrypt it using a tool called aescrypt.
Save | Cancel
Dylan, Thanks. I tested this on many files and directories and put simply it does the job it's intended for without any problems. Perhaps some people think it could do with a bit of fine tuning but as it stands no complaints here. Keep up the good work.
Save | Cancel